Distributed technology must know at all times what the latest contribution is while handling conflicts appropriately; Renitent ARTS, self-aware track versioning, and arcane extracts the correct version for the correct right granted. As renitent is per-file versioning cannot be trusted to the File System or a Distributed Revision Control System i.e. git, instead atomic ideompent changes are necessary
Data within your ownership that has power to be Arcane, Revisive, Trustless, Self-Aware {ARTS}
-- Renitent

The only thing man is capable of making is art
-- CyviZen coFounders
Data and Computing
The humble computer has embedded itself into every aspect of our daily lives, it has come a long way from planet scale mechanical machines to its current incarnation of nano-computers Data is the raw form of information it comes in two categories: Quantitative & Qualitative while information is structured to some relevant degree. Humans can memorize both data & information yet information is used in our conversations while data weighs our internal opinions (Opportunity Cost Doctrine). Humans can hold vast amounts of information and data with no upper limit yet discovered, yet we also for efficacy sake maintain a four quadrant Rumsfeld Matrix;
- known knowns: information we are aware of and understand
- known unknowns: information we know exists but have yet to understand, people see these as gaps in knowledge that can be addressed if desired through research, investigation of consultation with experts
- unknown knowns: information we know but are unaware of it, our minds place knowledge here for a myriad of reasons that can be frustrating due to its elusiveness to critical thinking
- unknown unknowns: information we have no idea about, and are unable to know, innate curiosity drives reduction of the overwhelming quantity of this information
Humanity discovered relatively early the known to unknown classification of our mind requires an external record to ensure continual linkage of unknown knowns to known knowns the challenge is navigating and searching such a record as it grows exponentially with life experience, a single notebook is insufficient, and chronological storage requires knowledge of times & dates for discovery which conflicts with humans mnemonic memory. Computers naturally suit this need which is why they have cyclically appeared throughout history
The primary purpose of computing is adaption as an external memory for humanity to actively minimise unknown knowns and maximise known knowns
To a computer everything stored is data, just 1s and 0s (or in Quantum Atomics -1, 0, +1 which is compressed 1 & 0).


Information Structuring
'This is the Unix philosophy: Write programs that do one thing and do it well. Write programs to work together. Write programs to handle text streams, because that is a universal interface.'
-- Douglas McIlroy, former head of Bell Labs Computing Sciences Research Center
Write programs to handle text streams, because that is a universal interface: this is the challenge, the inflection point between data and information, humans uplift data to information through language, in fact all human communication requires language
Any organization that designs a system (defined broadly) will produce a design whose structure is a copy of the organization's communication structure.
Genesis 1 shares the story of creation, words defined the communication structure, and thus the creation as defined by the creator follows in the design of the creator
Why does this matter? Because humanity uses computers, and computers are data processors assisting information to be known known or known unknowns instead of unknown unknowns or unknown knowns making them one of the most beneficial and powerful tools for humanity in existence!
Text streams are information, not data (remember to a computer data is just 1 and 0 & qualitative or quantitative structuring of any kind, is information not data). This is also the point where tradition interferes
- Humans record information on physical medium, say a sheet of paper
- Humans curate relevant to us information together, say a journal as several sheets of paper
- Humans store multiple journals together, say in a folder or shelf in a bookshelf
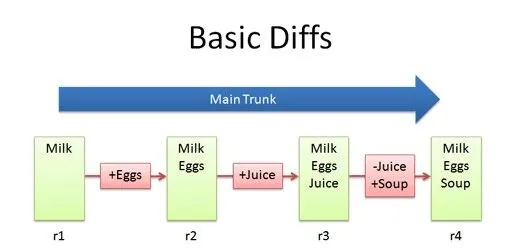
Versioning
Data exists at collection, it may not exist forever by nature as data is ephemeral, and thus by nature information may also be ephemeral; Yet information is also a collection, and thus must be mutable or able to be contributed to and curated over time
Versioning is not Journaling, where the file system maintains a log of changes prior to batch writing to the storage medium, versioning is a form of revision control that is transparent to users without the commit step revision control has
Versioning is not backup, changes occur on file change, not timers, versioning is per-file while backup is system-wide
NILFS is a log-structured file system supporting versioning of the entire file system and continuous snapshotting, which allows users to even restore files mistakenly overwritten or destroyed just a few seconds ago.
-- NILFS
Unfortunately NTT Laboratories have not prioritized important File System features with additional discussion available via lwn
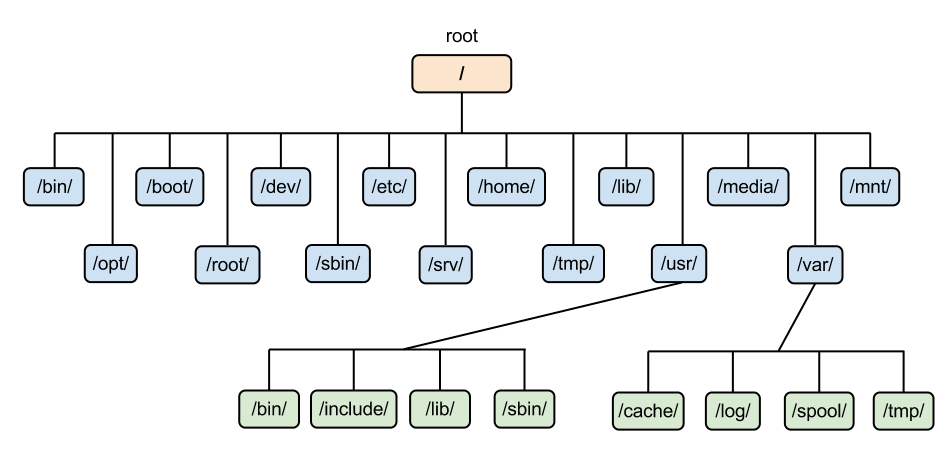
File Systems
File Systems for computers were created based on this approach where every reference point can be a file or folder and a folder may contain additional reference points
But information does not work this way, nothing exists in isolation!
File Systems fail to relate information correctly beyond basic structuring, Unix style systems addressed this by creating symlinks where the same file or folder may have references in multiple locations pointing to the same source
Databases attempted to restructure the file itself into relations, rows, columns, tables and joins to relate tables together
Eelco Dolstra in his 2003 paper demonstrated the failings of File System approaches to information management, that while databases had moved onto graphs (many-to-many relationship) operating systems were stuck with file system approach, Eelco approach is phenomenal in that it operates within the constraints of current Operating System history & design
Renitent, however, is the re-imagining of the file system entirely
To be clear, Renitent is not replacing a File System, it is the re-imagining of files & their structured information universally independent as ARTS. A file is self-aware, but integrates into the operating system environment such that the chosen File System is unaware of the files latent Renitent ability
Renitent could have created an entirely new Operating System, File System, et al but this would have required new capability in hardware. An impossibly difficult adoption path; Occam's Razor paired with Opportunity Cost Doctrine and UNIX philosophy implied Renitent best integrates with existing technological approaches where possible despite independence of them.
Renitent ARTS are arcane information is unknown by design. Data needs, a file system for presentation and interface into UNIX style Operating Systems, but Renitent data has no requirement to map to physical blocks on a storage device as traditional file systems do
Intellectual Property
Intellectual property (IP) includes inventions, designs, and other kinds of works of art created by the human brain and subject to copyright law
-- ARM
The financial impact of IP theft can be immense. Intellectual property can constitute more than 80% of a single company’s value, and its loss can trigger a cascade of fiscal consequences. The Commission on the Theft of American Intellectual Property estimates that annual costs from IP loss — which can include trade secret theft, the sale of counterfeit goods, and software piracy — range from $225 billion to $600 billion, or about 1% to 5% of the US GDP...
Intellectual property cases are one of the most costly kinds of law practiced in the United States. The cost of a patent infringement case with $10 million to $25 million at stake may range from $2 million to $9 million, and even intellectual property mediation costs an average of $100,000 per case...

Copyright and Patents
IP Press & Squire Patton Boggs explain that Copyright protection is not automatic, or globally applicable. Countries must also be party to one of several of the following conventions for Copyright to have legal standing:
- The Berne Convention (Berne)
- The Universal Copyright Convention (UCC)
- The Rome Convention (Rome)
- The WIPO Copyright Treaty (WCT) (TRIPS Agreement)
- Digital Millennium Copyright Act (DMCA)
Copyright exists in two primary forms:
- Published: Requires copies of previously unpublished work disseminated. i.e. Author writes a manuscript and sends a few friends copies to review
- Unpublished: Requires original work & evidence of knowledge of such work shared with other people. i.e. Author writes a manuscript and hands it to a few friends to read
Copyright provides legislative ground for argument around what conditions Intellectual Property could be copied, and what could constitute a breach against known and unknown technological methods. For instance some courts have ruled that copying Intellectual Property from Disk to RAM may be a copy for purposes of Copyright Legislation. (A technical act completed on your behalf by most operating systems)
Private But Eventually Public: Why Copyright in Unpublished Works Matters in the Digital Age illustrates the new direction the EU (and others) are taking to modern Copyright, per Copyright Term Directive 1993 dissemination of digital works after death of individual is encouraged and carries no breach of Copyright
Copyright is further complicated by End User License Agreements & Terms & Conditions of Use for software in which the work of art was created. Many now claim exclusive global license of content passing through their software en-route to the storage location, or use proprietary patented or copyrighted file-formats exclusively used by their software.
USA introduced Clarifying Lawful Overseas Use of Data (CLOUD) act which vaporizes data sovereignty if in accessing or storing your data any provider of software or infrastructure is a USA Company. Guaranteeing copies of this data will exist within USA Government and or agency systems
Specifically on Patents, if classified in the interest of national security, they can be seized by relevant Governments, virtually obliterating any ability to use the creative work. This is exactly what happened to Metal Storm Limited, and a significant reason behind open sourcing Parallella technology
Trade Secrets
All Intellectual Property starts as a Trade Secret per World Intellectual Property Organisation: {summary of Article 39 of the Agreement on Trade-Related Aspects of Intellectual Property Rights (TRIPS Agreement)}
- Commercially valuable because it is secret,
- be known only to a limited group of persons, and
- be subject to reasonable steps taken by the rightful holder of the information to keep it secret, including the use of confidentiality agreements for business partners and employees
Weak data security measures may significantly impact the outcome of legal action in IP theft cases. Some courts may calculate a company’s Net Present Value of Future Sales at zero if that company failed to take proper administrative, physical, and technological actions to safeguard their own intellectual property. In the absence of proper IP stewardship, judges have ruled, organizations risk forfeiting their trade secrets entirely.
-- ShardSecure
Commercially most Trade Secrets are only identified as potential Trade Secrets long after exposure or alternative Intellectual Property registration methods are pursued. CyviCo recognises it is quite challenging to identity the need to protect via Trade Secret without necessarily knowing what should be protected yet.
World Intellectual Property Organisation specifies that at this time only 13 out of 193 member states have varying legislative protocols to support Trade Secrets. Additionally most Operating Systems are starting to regularly take screenshots & use the local Artifical Intelligence for analysis to
help users easily find and remember things they've seen on their PC by taking snapshots of their screen and organizing them into a searchable timeline, essentially acting as a 'photographic memory'
-- Microsoft 'Recall'
World Intellectual Property Organisation, speaks to the protection of trade secrets as depending on 'honest commercial practices':
Trade secrets only protect their owner from unauthorized uses of its confidential information in a manner contrary to honest commercial practices.
Honest commercial practices refers to the absence of industrial or commercial espionage, breach of contract, breach of confidence and inducement to breach. Ironically Trade Secrets can only be secret if the secret is kept to a limited group of people. Technologies such as Microsoft Recall & Apple Intelligence by recording by their very nature expose the secret beyond the limited tracked copies or knowledge holders.
There is no protection if the same information is acquired by another through, for example, independent development or reverse engineering by others, or leakage of confidential information because the owner failed to take reasonable steps to keep it secret, or if the secret becomes generally known within the relevant industry circles.
-- World Intellectual Property Organisation
Reverse engineering generally doesn’t violate trade secret law because it is a fair and independent means of learning information, not a misappropriation.
-- Electronic Frontier Foundation - Reverse Engineering FAQ
Fair competition between enterprises is considered as the essential means for satisfying the supply and demand of the economy, and serving the interests of the consumers and the society as a whole... The law of unfair competition, including trade secret law, is considered necessary to ensure the fair functioning of the market and to promote innovation by suppressing anti-competitive business behaviors.
-- World Intellectual Property Organisation - Why is trade secret protection necessary
All creative work by default is internationally agreed to have No License, making all work (art) under exclusive copyright by default, nobody else can copy, distribute, or modify the work without being at risk of take-downs, shake-downs, or litigation
- Copyright and Patents apply to the finished work, not work in progress
- Trade Secrets require strict control of information and assurance only a select group of people are privy to such information
- There is no legislative framework to protect against reverse engineering
That being said, Copyright is not enforceable beyond No License (including original author) digitally as:
- the original work resides in ephemeral RAM and is destroyed,
- the saved file on-disk is a copy of the original,
A valid copyright claim requires verification of the original (now destroyed) work to the court
Renitent ARTS are arcane, revisive, and trustless by nature the contents within a file are unknown, by nature only those on the list are able to access the information within the file, by nature even if Renitent falls into adversarial hands the information is not exposed. All aspects of Trade Secret protection are embodied natively within Renitent ARTS
Renitent, is the only technology capable of protecting Trade Secrets, of providing prima facie evidence at any court as to ownership of data.
Access Control
File Systems work in tandem with the Kernel to enforce permissions via Access Control Lists {ACL}; three basic permissions read, write, execute; mapped over six tags (for simplicity in explanation only 3 tags are discussed as others are combinative)
- user by id
- group by id
- other
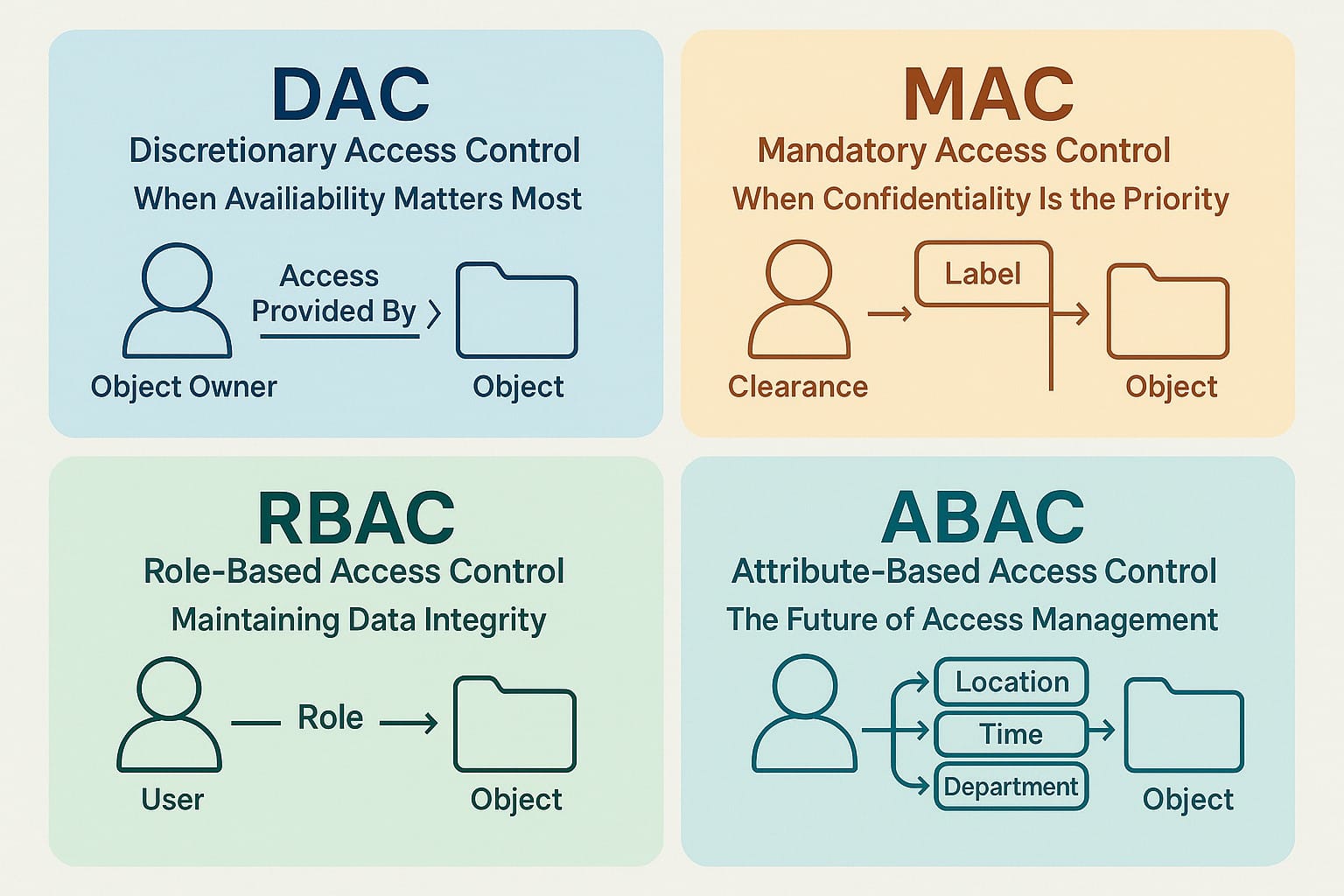
Access Control Lists, require one or more centralized Access Control Entities {ACE} for configuration and management
It is possible to give fine grained access control to any user or group under control of the Operating System using ACL lists. However, there are no guarantees that different computers have their Operating Systems configured exactly the same way, or that this user on the operating system may be exist or have access to the files on another computer. Microsoft Windows uses domains via Active Directory to provide more global objects for permissions to attach to than just the local file system; Lightweight Directory Access Protocol {LDAP} can do similar
The fundamental problem with ACL at the Computer or Active Directory is centralization
Access Control solutions require three main principles:
- Authentication {authn}: access, possesses a key to lock
- Authorization {authz}: control, known by controller
- Audit: independent review to establish state of system controls
Distributed Access Control
Securing distributed systems: A survey on access control techniques for cloud, blockchain, IoT and SDN summarise the popular access control approaches as of 2023, it should be noted, that none of the solutions presented are distributed in nature. The best approach discussed is Attribute Based Access Control {ABAC} yet as the authors mention auditing is challenging as no individual users permissions may be looked up and all objects must be checked against access policy
ABAC is the closest to a distributed approach to access control in that the objects may have permission checks and subjects permission checks but it also is not distributed in that related or overlapping attributes are necessary to grant access and centralized lists are required to track and monitor these overlaps
Blockchain is not distributed it falls within (de)centralized architecture.

Administrator, the overlooked vulnerability
There is a saying in CyberRisk (used to be called CyberSecurity but the industry realised they are unable to secure anything)
Blackmail always works
-- CyberRisk (Anonymous)
This means that whoever has control of the local administration account {root} or LDAP user with administration permissions is now a liability to all information on all accounts within reach
To make matters worse, other computer root accounts can mount the filesystem and modify ACL without restriction as their Operating System grants permission to do so, even if the physical storage was original configured against another Operating System
Centralization is the bane of responsibility & renitent style technology
-- CyviZen coFounders
Read, write, execute are an important part of UNIX style systems, and provided the ACE is capable of being properly secured. An effective mechanism of implementing per-file and per-folder permissions.
Renitent ARTS are trustless and self-aware any ACE introduces a trust failure point and would break the ARTS; The other problem with permissions is autonomy. Needing to ask something for permission to do something is not responsibility, but restriction, irrespective of if the trustworthiness of the thing being asked permission
Renitent has the following rights available to every file:
- author(s): no rights, permanent record for posterity and responsibility
- owner(s):
- right to leave as owner
- right to vote to modify rights of others
- right to add owner, gazer, contributor
- right to remove contributor
- gazer(s): right not obligation to see information in file
- contributor(s): right not obligation to modify or contribute information into file
Files or independent informational packets of data maintain authn & authz themself:
- owners can see authz and history
- gazers are presented with an immutable snapshot of the file
- contributors are presented with the latest mutable file state
Renitent is self-aware of all locations, copies of the same file and which locations contains the latest contributions
Against Malicious Intent {Espionage}
Cyber Espionage is an US$8 Trillion industry growing at 170% per annum.
If Cyber Espionage were an country, it would be the 3rd largest in the world by Gross Domestic Product (GDP)
State-sponsored economic cyber-espionage for commercial purposes: tackling an invisible but persistent risk to prosperity deep dives into who pays for Cyber Espionage, the benefits, and actors paying or funding the operations. They identify that 70% of all Cyber Espionage operations are local state government funded
Take a moment for this information to sink in; Cyber Espionage is US$8 Trillion, primarily targets commercial sector, growing at 170% and 60% of operations are funded by state sponsored actors irrespective of which country you reside in
Projects such as Zero Day Clock show that Ai technology has rapidly accelerated vulnerability and exploit times while RadWare maintains an live threatmap aggregating attacks they are defending against
It is not a matter of if data gets extracted from your control, it is a matter of when

The best case scenario for espionage, is that data was extracted by ransomware as then you know it was taken and may be able to recover some via payment. Sophos State of Ransomware 2025 identifies that even if paid, 15-20% of ransomed data is not recovered. The missing data is typically Trade Secret types of Intellectual Property sold on the black market to highest bidder.
For this reason technologies such as Confidential Computing were invented to ensure data processed on cloud computers was protected against the host operating system, and WireGuard to protect network data
Renitent ARTS take anti-espionage to an unprecedented level, Renitent is natively resilient against ransomware, to the point of being virtually immune due to its self-aware status.
Ransomware attempts several manouvers:
- encrypt files - Renitent actively monitors for entropy rejecting encryption
- extract data remotely - Renitent can only be opened by those on the access list, Renitent does not leak list information
- delete files - Renitent is distributed and append only, data never exists solely in a single location and knows whom made the last change
Data within your ownership that has power to be Arcane, Revisive, Trustless, Self-Aware {ARTS}
-- Renitent
In reviewing prior information, we gain an understanding of the importance, uniqueness and power available to those whom use Renitent ARTS.
While Renitent is seen by computers as data, it is crafted for information managed by those of mankind. Renitent is not suitable for Ai, machines, or abstract data processing.
Companies can use renitent to prove ownership but verification of humanity is required to access the information held within a renitent file as owners control the data, but cannot access it themself. They must be a contributor or gazer.
Renitent contains the following logical components working in tandem alongside a Digital Self in delivering the access rights of individuals to their information
Digital Self
EEZY is a technology built on renitent that provides digital self capability per renitent needs. An EEZY identifier is 21 alpha-numeric characters in length. It is necessary to provide EEZY as part of the process to access renitent files.
Renitent requires people, every file has an author, owner, contributor and gazer.
Renitent integrates and requires a digital self for such tasks where a digital self verifies humanity constantly and curates a forest of renitent urns presenting the correct file to your self upon request


urn
An identifiable location in CyverSpace. Location does not mean a physical reference to a sever or location in a filesystem. Renitent is a distributed technology; location is simply a point that Renitent can locate even if the data or pieces of it reside on multiple machines, multiple servers, or cloud storage systems.
- Urns use only lowercase letters and numbers with no special symbols
- Urns are extremely low collision and have no centralized point of generation, any renitent enabled operating system can generate a new Urn
- Urns are cryptographically secure, it is not possible to identify a prior or next Urn in a sequence as audited by security experts and Artificial Intelligence where they are considered safe to use for sharing secrets between systems
- Urns have no upper limit on length, Renitent reserves the following lengths for technology built on Renitent:
- 12 Renitent apps
- 21 EEZY
Adversaries may think they could start at 0(n) and incrementally request urn; but by nature every new urn may create within a sequence they already scanned as empty. Thus rendering constant and continual scanning of such a large identifier range impractical. The nature of Renitent day-to-day use is such that it is infrequent to request an urn that does not exist; and such systems can be blacklisted even at Denial Of Service (DOS) scale.
Urns with your digital self are important for ownership:
- digital selfs cannot inhabit a system without your self controlling the system
- every digital self has an urn their information resides in, this urn is available on any system that digital self inhabits
- urns are self to self by nature; a new urn is created for data shared between multiple digital selfs (for those whom have owner rights)
- should an owner voluntarily remove themself or by mutual consent be removed; a different urn will hold the data, and the old will be void thus the entire tree may be transplanted between urns as required
roots
Renitent is natively ransomware resilient (virtually immune to ransomware), Renitent puts roots down into any filesystem that can guarantee physical blocks have not been modified.
- Roots interface the traditional File System Structure with Renitent
- Roots monitor entropy, any attempt to encrypt renitent files is rejected
- Roots determine which part of the trunk is visible
- Roots know which distributed system has the latest changes for any file, irrespective of the files distributed across many machines
- Roots will sync the latest file changes on-demand optimising bandwidth
For those familiar with Peer2Peer systems, roots handle the networking, delta transmission, and synchronisation of urns as files are requested or appended to.
trunk
Is the versioning component of Renitent. It is an identity aware append only log, that knows who made a change, and on which fingerprinted hardware the change was made on.
At all times a linked-list style log of changes can be observed for a renitent file
Changes can be re-wound by mutual consent of owners, this protects against the spam style ransomware attack.
branches
Are where contributions occur, they can cross fuse with other branches and be pruned at any time.
While Renitent is more akin to a log-structured file system, branches and trunk terminology from version control systems has similar concept; in that contributors exist on a branch and their contributions append into the trunk as appropriate.
Branches can exist as read-write (contributor) or read-only (gazer)
Renitent requires the operating system to disable clipboard functionality when gazer views a Renitent file.
grafts
While the location of an urn matters for data access and is the primary interface for owners; branches graft together with contributors and gazers to provide the information they are permitted.
Urns collect files, but each graft is unique to a file, as such it is possible that a contributor or gazer may only have access to a few files in an urn and they would have no knowledge of any other files within the urn.
Only owners have knowledge of all renitent files within an urn, but no access to their contents.


leaves
Renitent is ephemeral as information and data are ephemeral. It is possible to shred any file irrespective of where that file may reside, even on systems outside of your control.
Renitent considers all files to be ephemeral. Ephemerality is determined by the owners and enforced by Renitent. A file without ephemeral information shreds at the end of time.
fruit
In an ideal world, Renitent would be the universal and ubiquitous data standard. It is the only technology able to prima facie prove ownership. We do not live in an ideal world, and sometimes files need to be sent to people or machines that do not have renitent capability.
Operating Systems without Renitent capability are; unable to prove ownership of data, or information, or protect files from ransomware, or legally protect files. (all standard ransomware approaches involve out of band backups, and do nothing to protect against extraction of files).
Should it be imperative that a file leave renitent control, renitent creates a fruit. This fruit is stripped of its renitent protections and rights. This fruit is fingerprinted, stenographic techniques applied, and made immutable to permanently capture the point in time & state of information of the file. Contributions can continue to a renitent file after fruit is created, but a new fruit would need to be created, should the new contributions also need to be shared to non-renitent systems.
Visual slice of the forest
In the picture, you will notice a digital self wandering through the forest looking for requested files. Imagine for a moment that you are standing where they are, when looking you can see an ordered row of renitent urns with trees, branches, leaves, fruit.
This slice of what you visually see, is what is merged and overlayed to the operating system as a normal file system folder. In other words a folder may be composed of many renitent urns, and their branches or leaves or fruit where some parts are immutable and others not.
This slice enables behaviours such as:
- selective immutability
- ephemeral overwriting of renitent files i.e. personal customisations in an immutable system
- sensitive data broken into many different urns with unknowable access or scope of entire data by those who lack knowledge and access of all urns
- placing multiple contributors behind your own contribution, such that even if they shred their work is does not affect yours
Renitent has existed for almost a decade, its files have been displayed on community notice boards, stored in public Git repositories and have been Quantum Decryption protected since inception.
A bounty of 250,000 Cy (and permanent work offer) is available to anyone who can prove a Renitent file has been breached.
- Renitent: immune to external affects
- continuously observe and analyze their data and operational state to detect changes in quality and performance
- right: sanction of independent action; can be exercised without permission of something; responsible
- permission: must request authority from something prior to undertaking an action, may be revoked at any time; removes freedom